Tunneling provides a mechanism to transport packets of one protocol within another protocol. The protocol that is carried is called as the passenger protocol, and the protocol that is used for carrying the passenger protocol is called as the transport protocol. Generic Routing Encapsulation (GRE) is one of the available tunneling mechanisms which uses IP as the transport protocol and can be used for carrying many different passenger protocols. The tunnels behave as virtual point-to-point links that have two endpoints identified by the tunnel source and tunnel destination addresses at each endpoint.
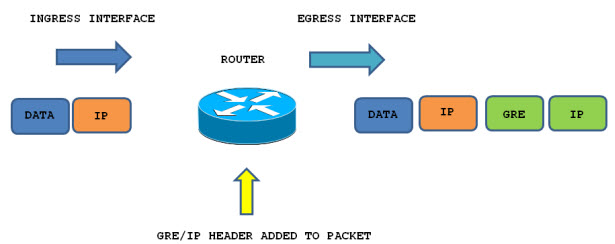
The below diagram shows encapsulation process of GRE packet as it traversers the router and enters the tunnel interface:
Configuring GRE Tunnel:
Configuring a GRE tunnel involves creating a tunnel interface, which is a logical interface. Then you must configure the tunnel endpoints for the tunnel interface.
To configure the tunnel source and destination, issue the tunnel source {ip-address | interface-type} and tunnel destination {host-name | ip-address} commands under the interface configuration mode for the tunnel.
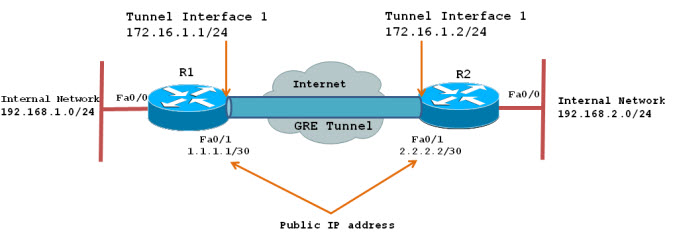
The below example explain about how to create simple GRE tunnels between endpoints and the necessary steps to create and verify the GRE tunnel between the two networks.R1’s and R2’s Internal subnets(192.168.1.0/24 and 192.168.2.0/24) are communicating with each other using GRE tunnel over internet. Both Tunnel interfaces are part of the 172.16.1.0/24 network.
First step is to create our tunnel interface on R1 and R2 :
| R1 | R2 |
| R1(config)# interface Tunnel1
R1(config-if)# ip address 172.16.1.1 255.255.255.0 R1(config-if)# ip mtu 1400 R1(config-if)# ip tcp adjust-mss 1360 R1(config-if)# tunnel source 1.1.1.1 R1(config-if)# tunnel destination 2.2.2.2 |
R2(config)# interface Tunnel1
R2(config-if)# ip address 172.16.1.2 255.255.255.0 R2(config-if)# ip mtu 1400 R2(config-if)# ip tcp adjust-mss 1360 R2(config-if)# tunnel source 2.2.2.2 R2(config-if)# tunnel destination 1.1.1.1 |
Since GRE is an encapsulating protocol, we adjust the maximum transfer unit (mtu) to 1400 bytes and maximum segment size (mss) to 1360 bytes. Because most transport MTUs are 1500 bytes and we have an added overhead because of GRE, we must reduce the MTU to account for the extra overhead. A setting of 1400 is a common practice and will ensure unnecessary packet fragmentation is kept to a minimum.
After configuring tunnel, two tunnel endpoints can see each other can verify using an icmp echo from one end.
R1# ping 172.16.1.2
Type escapes sequence to abort.
Sending 5, 100-byte ICMP Echos to 172.16.1.2, timeout is 2 seconds:
!!!!!
Success rate is 100 percent (5/5), round-trip min/avg/max = 1/2/4 ms
Workstations on either network will still not be able to reach the other side unless a routing is configure on each router.Here We will configure static route on both router.
R1(config)# ip route 192.168.2.0 255.255.255.0 172.16.1.2
R2(config)# ip route 192.168.1.0 255.255.255.0 172.16.1.1
Now both networks (192.168.1.0/24 and 192.168.2.0/24) are able to freely communicate with each other over the GRE Tunnel.
More Details:
Here is a sample config for GRE.
GRE TUNNEL
Consider the following topologyRouter1 [S0](64.45.15.17) —— Internet ——-(65.17.89.11)[S0]Router2—192.168.1.0/24
|_(10.0.0.1)_____________GRE Tunnel____________________(10.0.0.2)_|Router1
*******interface Tunnel0
ip address 10.0.0.1 255.255.255.252
tunnel source 64.45.15.17
tunnel destination 65.17.89.11Router2
*******interface Tunnel0
ip address 10.0.0.2 255.255.255.252
tunnel source 65.17.89.11
tunnel destination 64.45.15.17And just apply the necessary routes for those tunnels:
for example
ip route 192.168.1.0 255.255.255.0 Tunnel0About Keepalives here is the information:
Router1(config)#interface Tunnel1
Router1(config-if)#keepaliveBy default, this keepalive command sends a packet through the tunnel to check its status
once every 10 seconds. If there is no response to three successive polls, the router
declares the tunnel interface to be down. So, this will change the tunnel’s status about
30 seconds after a failure.You can adjust both the time interval and the number of retries. For example, to send a
keepalive packet every five seconds, but to keep the default three retry limit, you could
use the following command:Router1(config)#interface Tunnel1
Router1(config-if)#keepalive 5If you want to change the number of retries, you can specify the new value after the time
interval. The following example will send a keepalive packet every three seconds, and will
declare the tunnel down if it doesn’t hear a response back to two successive keepalive
tests:Router1(config)#interface Tunnel1
Router1(config-if)#keepalive 3 2
— Examples and Tips from https://supportforums.cisco.com/
More Related Guide: